Malwarebytes removal log
A Malwarebytes log of removal will look similar to this:
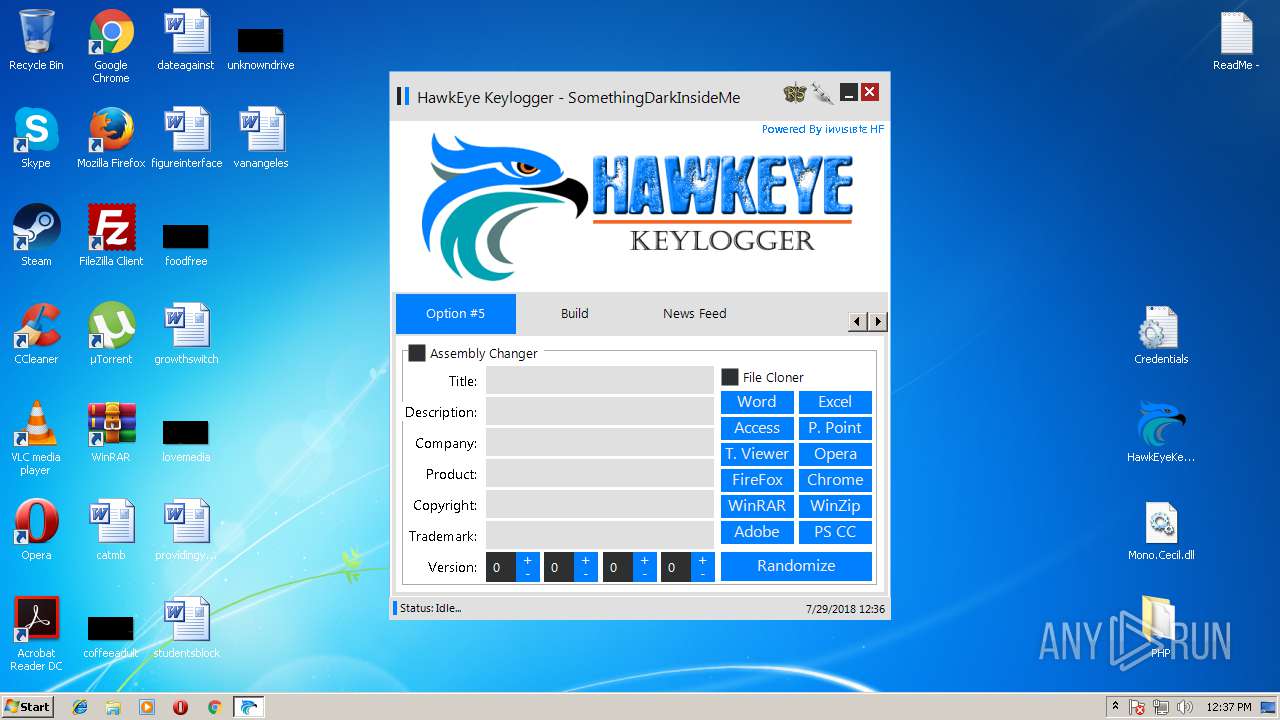
.leto ransomware decryptor download 'brute force ssh key' @n twitter hack 0 day exploit download 00 01 0day link exploit 100 100% fud crypter 100% fud doc exploit 100% fud crypter free 1000 free youtube subscribers 1000 free youtube subscribers app 1000 free youtube subscribers bot 10000 13 14 16 1st mass mailer free download 20 2. However, instead of coronavirus drug advice, the executable actually is a HawkEye keylogger loader with anti-VM and anti-sandbox capabilities that will attempt to turn off Windows Defender via.
Malwarebytes
www.malwarebytes.com
-Log Details-
Scan Date: 3/27/18
Scan Time: 12:22 AM
Log File: 35f8ee73-3187-11e8-80eb-00ffc8517b86.json
Administrator: Yes
-Software Information-
Version: 3.4.4.2398
Components Version: 1.0.322
Update Package Version: 1.0.4502
License: Premium
-System Information-
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: DE-WIN7Fwiplayer
-Scan Summary-
Scan Type: Threat Scan
Result: Completed
Objects Scanned: 296004
Threats Detected: 9
Threats Quarantined: 0
(No malicious items detected)
Time Elapsed: 3 min, 4 sec
-Scan Options-
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Disabled
Heuristics: Enabled
PUP: Detect
PUM: Detect
-Scan Details-
Process: 1
PUP.Optional.ArdamaxKeyLogger.Generic, C:PROGRAMDATAXDUSAUBST.EXE, No Action By User, [7307], [260508],1.0.4502
Module: 1
PUP.Optional.ArdamaxKeyLogger.Generic, C:PROGRAMDATAXDUSAUBST.EXE, No Action By User, [7307], [260508],1.0.4502
Registry Key: 0
(No malicious items detected)
Registry Value: 1
PUP.Optional.ArdamaxKeyLogger.Generic, HKLMSOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUN|BST START, No Action By User, [7307], [260508],1.0.4502
Registry Data: 0
(No malicious items detected)
Data Stream: 0
(No malicious items detected)
Folder: 0
(No malicious items detected)
File: 6
PUP.Optional.HawkEye, C:USERSFWIPLAYERDESKTOPHAWKEYE.LNK, No Action By User, [4609], [245599],1.0.4502
PUP.Optional.ArdamaxKeyLogger.Generic, C:PROGRAMDATAXDUSAUBST.EXE, No Action By User, [7307], [260508],1.0.4502
Spyware.KeyLogger, C:USERSFWIPLAYERAPPDATAROAMINGMicrosoftWindowsRecentBST.01.lnk, No Action By User, [3808], [80844],1.0.4502
Spyware.KeyLogger, C:PROGRAMDATAXDUSAUBST.01.EXE, No Action By User, [3808], [80844],1.0.4502
PUP.Optional.ArdamaxKeyLogger, C:USERSFWIPLAYERAPPDATAROAMINGMicrosoftWindowsRecentBST.02.lnk, No Action By User, [3611], [86580],1.0.4502
PUP.Optional.ArdamaxKeyLogger, C:PROGRAMDATAXDUSAUBST.02.EXE, No Action By User, [3611], [86580],1.0.4502
Physical Sector: 0
(No malicious items detected)
(end)
Hardware keyloggers are used for keystroke logging, a method of capturing and recording computer users' keystrokes, including sensitive passwords.[1] They can be implemented via BIOS-level firmware, or alternatively, via a device plugged inline between a computer keyboard and a computer. They log all keyboard activity to their internal memory.
Description[edit]
Hardware keyloggers have an advantage over software keyloggers as they can begin logging from the moment a computer is turned on (and are therefore able to intercept passwords for the BIOS or disk encryption software).
Hawkeye Keylogger

All hardware keylogger devices have to have the following:
- A microcontroller - this interprets the datastream between the keyboard and computer, processes it, and passes it to the non-volatile memory
- A non-volatile memory device, such as flash memory - this stores the recorded data, retaining it even when power is lost
Generally, recorded data is retrieved by typing a special password into a computer text editor. The hardware keylogger plugged in between the keyboard and computer detects that the password has been typed and then presents the computer with 'typed' data to produce a menu. Beyond text menu some keyloggers offer a high-speed download to speed up retrieval of stored data; this can be via USB mass-storage enumeration or with a USB or serial download adapter.
Typically the memory capacity of a hardware keylogger may range from a few kilobytes to several gigabytes, with each keystroke recorded typically consuming a byte of memory.
Types of hardware keyloggers[edit]
- A Regular Hardware Keylogger is used for keystroke logging by means of a hardware circuit that is attached somewhere in between the computer keyboard and the computer. It logs all keyboard activity to its internal memory which can be accessed by typing in a series of pre-defined characters. A hardware keylogger has an advantage over a software solution; because it is not dependent on the computer's operating system it will not interfere with any program running on the target machine and hence cannot be detected by any software. They are typically designed to have an innocuous appearance that blends in with the rest of the cabling or hardware, such as appearing to be an EMCBalun. They can also be installed inside a keyboard itself (as a circuit attachment or modification), or the keyboard could be manufactured with this 'feature'. They are designed to work with legacy PS/2 keyboards, or more recently, with USB keyboards. Some variants, known as wireless hardware keyloggers, have the ability to be controlled and monitored remotely by means of a wireless communication standard.[citation needed]
- Wireless Keylogger sniffers - Collect packets of data being transferred from a wireless keyboard and its receiver and then attempt to crack the encryption key being used to secure wireless communications between the two devices.
- Firmware - A computer's BIOS, which is typically responsible for handling keyboard events, can be reprogrammed so that it records keystrokes as it processes them.
- Keyboard overlays - a fake keypad is placed over the real one so that any keys pressed are registered by both the eavesdropping device as well as the legitimate one that the customer is using.[2]
- Key commands - exist in much legitimate software. These programs require keyloggers to know when you’re using a specific command.[3]
Countermeasures[edit]
Denial or monitoring of physical access to sensitive computers, e.g. by closed-circuit video surveillance and access control, is the most effective means of preventing hardware keylogger installation. Visual inspection is the easiest way of detecting hardware keyloggers. But there are also some techniques that can be used for most hardware keyloggers on the market, to detect them via software. In cases in which the computer case is hidden from view (e.g. at some public access kiosks where the case is in a locked box and only a monitor, keyboard, and mouse are exposed to view) and the user has no possibility to run software checks, a user might thwart a keylogger by typing part of a password, using the mouse to move to a text editor or other window, typing some garbage text, mousing back to the password window, typing the next part of the password, etc. so that the keylogger will record an unintelligible mix of garbage and password text[4] See also Keystroke logging countermeasures.
The main risk associated with keylogger use is that physical access is needed twice: initially to install the keylogger, and secondly to retrieve it. Thus, if the victim discovers the keylogger, they can then set up a sting operation to catch the person in the act of retrieving it. This could include camera surveillance or the review of access card swipe records to determine who gained physical access to the area during the time period that the keylogger was removed.
Hawkeye Keylogger V5 Camera

References[edit]
Hawkeye Keylogger V5 Software

- ^'Keyloggers, pros and cons'. BCS.
- ^Jeremy Kirk (2008-12-16). 'Tampered Credit Card Terminals'. IDG News Service. Retrieved 2009-04-19.
- ^'What Are Keyloggers and How to Protect Against Them'. Safety Detective. 2018-09-02. Retrieved 2018-11-22.
- ^Hardware Keylogger DetectionArchived 2012-02-09 at the Wayback Machine, SpyCop.
External links[edit]